Android prime target for cyber criminals
ISTANBUL - Hürriyet Daily News

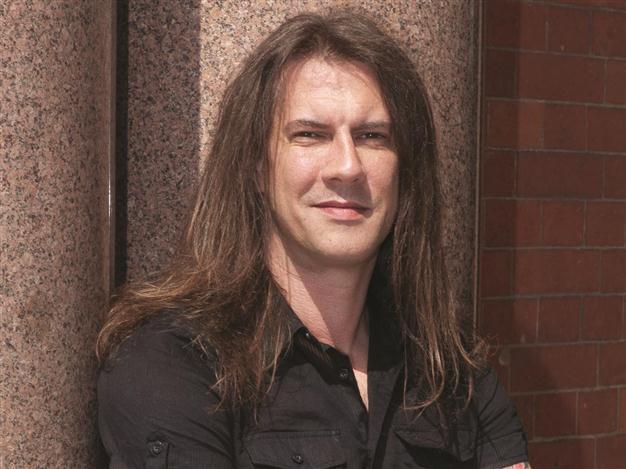
A new cyber threat is created every 3.5 seconds, says Ferguson of Trend Micro.
Mobile phones are increasingly being threatened by viruses as the smart phone market grows rapidly, according to an executive at Trend Micro, a prominent global provider of network antivirus and Internet content security software.
“The realm of mobile threats hit a peak in 2011,” Rik Ferguson, Trend Micro’s director of the security research and communication department, said yesterday, adding that smart phone and tablet platforms, especially
Android, would suffer from more cybercriminal attacks.
The most targeted platform is Android and the number of Android malwares will exceed 120,000 by the end of 2012, said Ferguson.
The reason the Android platform is more vulnerable to such attacks, according to Ferguson, is that Google, the issuer of the mobile operating system, does not control the applications supplied to the Android Market. Cyber criminals can attach spyware to the applications and republish them on the market where users download it to their smart phones. The Android market recently hit the 10 billion application download mark.
Other firms, such as RSA and Sony PlayStation, have also been targeted, causing problems for consumers, he said. Some 77 million Sony PlayStation users’ personal data was captured and the PlayStation network was shut down temporarily.
Complex vulnerabilities
The number of security vulnerabilities in the world fell from 4,651 in 2010 to 4,155 in 2011, according to official data, Ferguson said. However, cyber attacks have become more complex and multi-directional, he said, adding that this trend would continue in 2012 and grow more sophisticated. “A new threat is created every 3.5 seconds. [The risk of] data and financial loss is rising more than ever before,” he said.
An increasing number of workers use their own devices at work which makes it harder for information technology managers to ensure the security of corporate data since it is more difficult to monitor and provide security in a working environment where multi-operation systems are being used, according to Ferguson. k HDN
iPhone, smartphone,